- ホーム
- Cisco
- 200-201J - Understanding Cisco Cybersecurity Operations Fundamentals (200-201日本語版)
- Cisco.200-201J.v2024-04-30.q134
- 質問100
有効的な200-201J問題集はJPNTest.com提供され、200-201J試験に合格することに役に立ちます!JPNTest.comは今最新200-201J試験問題集を提供します。JPNTest.com 200-201J試験問題集はもう更新されました。ここで200-201J問題集のテストエンジンを手に入れます。
200-201J問題集最新版のアクセス
「452問、30% ディスカウント、特別な割引コード:JPNshiken」
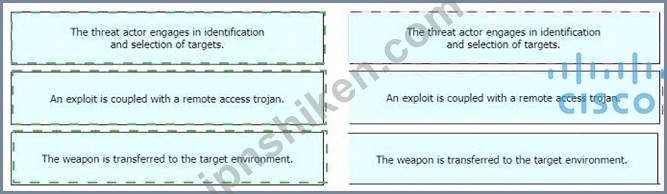
定義を左から右のフェーズにドラッグ アンド ドロップして、サイバー キル チェーン モデルに従って侵入イベントを分類します。


正解:
Explanation:
Delivery: This step involves transmitting the weapon to the target.
Weaponization: In this step, the intruder creates a malware weapon like a virus, worm or such in order to exploit the vulnerabilities of the target. Depending on the target and the purpose of the attacker, this malware can exploit new, undetected vulnerabilities (also known as the zero-day exploits) or it can focus on a combination of different vulnerabilities.
Reconnaissance: In this step, the attacker / intruder chooses their target. Then they conduct an in-depth research on this target to identify its vulnerabilities that can be exploited.
- 質問一覧「134問」
- 質問1 システム管理者は、特定のレジストリ情報が正確であることを確認
- 質問2 展示を参照してください。 (Exhibit) Wireshark 内で抽出可能な...
- 質問3 現在組織を標的にしている脅威を理解するために、組織はどの情報
- 質問4 バッファ オーバーフロー攻撃を防ぐアクションはどれですか?
- 質問5 SIEMとSOARの違いは何ですか?
- 質問6 エンジニアは、TCP 帯域幅の使用状況、応答時間、遅延を可視化し...
- 質問7 定義を左から右のフェーズにドラッグ アンド ドロップして、サイ...
- 質問8 PII データの不適切な使用または開示に関連するカテゴリはどれで...
- 質問9 SOAR と SIEM の違いは何ですか?
- 質問10 アナリストは、正当なセキュリティ アラートが無視されたことを
- 質問11 ある企業は、ネットワーク トラフィックの数ミリ秒の遅延が許容
- 質問12 NISTSP800-86によると。揮発性と見なされる2種類のデータはどれ...
- 質問13 イベントを調査する場合、データの漏えいが発生したかどうかを判
- 質問14 組織はいくつかのサードパーティ企業と協力しています。データ交
- 質問15 非対称暗号を使用する利点は何ですか?
- 質問16 (Exhibit) 展示を参照してください。攻撃者はNmapを使用してサー...
- 質問17 バッファオーバーフロー攻撃の説明は何ですか?
- 質問18 「色」と「色」に一致する正規表現は?
- 質問19 ネットワーク エンジニアは、外国政府が自国の防衛請負業者の 1 ...
- 質問20 ソーシャルエンジニアリング攻撃の説明は何ですか?
- 質問21 どのタイプのアクセス制御がユーザーの職務に依存しますか?
- 質問22 インライン トラフィック インタロゲーションとトラフィック ミ...
- 質問23 改ざんされたディスクイメージと改ざんされていないディスクイメ
- 質問24 エージェントレス保護と比較した場合、エージェントベースの保護
- 質問25 展示を参照してください。 (Exhibit) エンジニアが最近の違反後...
- 質問26 DDoS攻撃の2つのカテゴリを食べたのは何ですか? (2つ選択して...
- 質問27 エンジニアは、1 週間前にインシデント管理チームからのインシデ...
- 質問28 展示を参照してください。 (Exhibit) この Stealthwatch ダッシ...
- 質問29 ディープパケットインスペクションとステートフルインスペクショ
- 質問30 展示を参照してください。 (Exhibit) この PCAP ファイルには何...
- 質問31 展示を参照してください。 (Exhibit) このパケット キャプチャか...
- 質問32 これらのうち、セキュリティインシデントに関連するSOCメトリッ...
- 質問33 展示を参照してください。 (Exhibit) どのタイプの攻撃が実行さ...
- 質問34 調査のアトリビューションに必要な情報はどれですか?
- 質問35 攻撃ベクトルと攻撃対象領域の違いは何ですか?
- 質問36 展示を参照してください。 (Exhibit) ペイロードがクエリまたは...
- 質問37 セキュリティ オペレーション センターの有効性と範囲を評価する...
- 質問38 ネットワーク内外の攻撃者を想定し、組織内のシステムまたはリソ
- 質問39 左からアクセス制御モデルを右の正しい説明にドラッグ アンド ド...
- 質問40 展示する。 (Exhibit) エンジニアは、Web アプリケーションの速...
- 質問41 展示を参照してください。 (Exhibit) セキュリティアナリストが...
- 質問42 Web アプリケーションとの間で送受信されるすべてのメッセージの...
- 質問43 認証局はセキュリティにどのように影響しますか?
- 質問44 TapポートとSPANポートから取得したデータの違いは何ですか?...
- 質問45 セキュリティの概念を左側から右側のその概念の例にドラッグアン
- 質問46 セキュリティ エンジニアが、同じデータ センター内のファイルが...
- 質問47 ソーシャル エンジニアリング攻撃の例は何ですか?
- 質問48 展示を参照してください。 (Exhibit) このネットワークで何が起...
- 質問49 展示を参照してください。 (Exhibit) 攻撃者は企業のネットワー...
- 質問50 Windows システムのイベントがログ メッセージにイベント コード...
- 質問51 繰り返し使用するためにペイロードを保存せずに実行するクロスサ
- 質問52 脅威とリスクの違いは何ですか?
- 質問53 エンジニアは、入力および出力の境界トラフィックを復号化し、ネ
- 質問54 NIST SP800-617 に記載されているインシデント対応計画に含まれ...
- 質問55 攻撃を成功させるために必要なアクセス レベルをキャプチャする
- 質問56 展示を参照してください。 (Exhibit) 何が起こっているのですか...
- 質問57 HTTPS トラフィックの監視を困難にしている原因
- 質問58 脆弱性管理フレームワークの目的は何ですか?
- 質問59 展示を参照してください。 (Exhibit) この要求は、データベース...
- 質問60 展示を参照してください。 (Exhibit) この Stealthwatch ダッシ...
- 質問61 ディープパケットインスペクションとステートフルインスペクショ
- 質問62 ランサムウェアの機能である回避手法はどれですか?
- 質問63 すべてのプロセスを root または管理者として実行すると、どのセ...
- 質問64 アナリストは、HR部門のサーバーの1つで低下した処理能力に関す...
- 質問65 脅威とリスクの違いは何ですか?
- 質問66 エンジニアは、サンドボックス分析ツールで疑わしいファイルを実
- 質問67 SOCチームは、エンドポイントでの侵害の潜在的な指標を確認しま...
- 質問68 ホストベースのファイアウォールはワークステーションを何から保
- 質問69 随意アクセス制御(DAC)と役割ベースのアクセス制御(RBAC)の...
- 質問70 展示を参照してください。 (Exhibit) Wireshark内のTCPストリー...
- 質問71 脅威ハンティングとは何ですか?
- 質問72 どのイベントがビッシング攻撃ですか?
- 質問73 外部に面したデバイスにネットワーク トラフィックが大量に流入
- 質問74 サーバーにSyslog収集ソフトウェアがインストールされているログ...
- 質問75 CVSS によると、攻撃ベクトル スコアはどのように説明されますか...
- 質問76 最も多くのストレージ スペースを必要とするデータ収集のタイプ
- 質問77 展示を参照してください。 (Exhibit) この出力はどの Linux ログ...
- 質問78 攻撃の兆候を表すオプションはどれですか?
- 質問79 TORは転送中にデータコンテンツをどのように変更しますか?
- 質問80 調査員は、CDFS 形式で保存されている ISO ファイルのコピーを調...
- 質問81 非対称暗号化に対する対称暗号化の利点は何ですか?
- 質問82 展示を参照してください。 (Exhibit) この出力は、IP アドレスが...
- 質問83 Linux および Mac OS X オペレーティング システムを使用するオ...
- 質問84 低帯域幅攻撃はどの手法ですか?
- 質問85 コマンド アンド コントロール サーバーの機能は何ですか?
- 質問86 ある従業員が、誰かがシステムにログインして承認されていない変
- 質問87 エンジニアは、Nmap を使用して IDS デバイスで侵入ポートスキャ...
- 質問88 調査において属性の役割を担う資産はどれ? (2つ選んでください。...
- 質問89 セキュリティの専門家が、CDFS 形式で保存された ISO ファイルで...
- 質問90 アナリストはSIEMプラットフォームを使用しており、Ciscoデバイ...
- 質問91 左の要素を右のインシデント処理の正しい順序にドラッグ アンド ...
- 質問92 防御-m-深度戦略で使用される 2 つの手段はどれですか? (2つお選...
- 質問93 エンジニアは、NISTフレームワークとISOフレームワークを比較す...
- 質問94 どの攻撃がリソース枯渇の回避手法を表していますか?
- 質問95 展示を参照してください。 (Exhibit) どのような情報が描かれて...
- 質問96 左側のテクノロジを、右側のテクノロジが提供するデータ型にドラ
- 質問97 統計的検出と比較した場合のルールベース検出とは何ですか?
- 質問98 エンジニアは、重要なサーバーのパフォーマンスの低下に影響を与
- 質問99 ビジネスサービスに影響を与える可能性のあるセキュリティインシ
- 質問100 定義を左から右のフェーズにドラッグ アンド ドロップして、サイ...
- 質問101 展示を参照してください。 (Exhibit) どのタイプのログが表示さ...
- 質問102 アナリストは、さまざまなオペレーティング システムの機能を調
- 質問103 エンジニアは、既知の TOR 出口ノードを持つトラフィックがネッ...
- 質問104 SOC アナリストは、特定のセッションを識別している Linux シス...
- 質問105 エンジニアは、リモートサーバーが正常なセッションを確立できな
- 質問106 RC4 のようなストリーム暗号が同じキーで 2 回使用された場合、...
- 質問107 攻撃対象領域は攻撃ベクトルとどのように異なりますか?
- 質問108 セキュリティエンジニアは、既知の高度な持続的脅威グループに起
- 質問109 ゼロトラスト セキュリティ モデルは何を意味しますか?
- 質問110 展示を参照してください。 (Exhibit) コマンドの結果はどうなる...
- 質問111 ユーザーは、コンテンツを開く前に、標的を絞ったスピアフィッシ
- 質問112 展示を参照してください。 (Exhibit) どのアプリケーションレベ...
- 質問113 脆弱性への攻撃はどのように分類されますか?
- 質問114 暗号化の影響は何ですか?
- 質問115 ある組織は最近、既知のハクティビスト グループによるオンライ
- 質問116 どのプロセスがアプリケーションレベルの許可リストを表しますか
- 質問117 侵入者は悪意のある活動を試み、ユーザーと電子メールを交換し、
- 質問118 署名ベースの検出と動作ベースの検出の違いは何ですか?
- 質問119 オフライン監査ログには、システムの侵害につながる脆弱性を悪用
- 質問120 さまざまな事業部門間のインシデント対応の調整、損害の最小化、
- 質問121 ツールを使用して元のデータとコピーされたデータのメッセージダ
- 質問122 展示を参照してください。 (Exhibit) どのイベントが発生してい...
- 質問123 NetFlow ログ セッションの ACK フラグと RST フラグの違いは何...
- 質問124 開発者は、次の必要な結果を得るプロセスを作成できる Linux ツ...
- 質問125 サイバー攻撃者は、企業が使用しているソフトウェアのセキュリテ
- 質問126 エンジニアが、受信者によって機密文書が改ざんされて盗まれた最
- 質問127 攻撃の影響を受けるすべてのホストの特定を含むインシデント対応
- 質問128 TLS ハンドシェイクのネゴシエーション フェーズでクライアント...
- 質問129 最初の証拠から生じる理論または仮定を支持する証拠のタイプはど
- 質問130 2 つのサービス拒否攻撃とは何ですか? (2つ選んでください。)...
- 質問131 エンジニアは、プロキシ サーバーからログを取得し、受け取った
- 質問132 展示を参照してください。 (Exhibit) 疑わしい IP アドレスは、T...
- 質問133 展示を参照してください。 (Exhibit) このパケット キャプチャか...
- 質問134 ユーザーtom0411976943とdan1968754032の間の公開鍵の信頼できる...

